Edge vpn cbic: Edge VPN CBIC setup, Edge browser integration, privacy, security, performance, and compliance guide 2026
Edge vpn cbic edge vpn cbic setup edge browser integration privacy security performance and compliance guide
Edge vpn cbic edge vpn cbic setup edge browser integration privacy security performance and compliance guide — quick facts: a robust guide to getting VPNs on the Edge ecosystem, with a focus on CBIC requirements, browser integration, and practical steps you can implement today. This post serves as your comprehensive, beginner-to-advanced manual, and you’ll get clear instructions, real-world tips, and up-to-date data you can action now.
Quick Start Checklist:
- Identify your CBIC-compliant VPN provider and whether they offer Edge-ready profiles
- Install the VPN extension or configure a system-wide VPN on Windows for Edge
- Enable privacy- and security-focused features: kill switch, leak protection, DNS masking
- Test performance with speed and latency benchmarks
- Review compliance requirements and audit trails for your organization
What you’ll learn:
- Step-by-step CBIC-compliant setup for Edge
- How to integrate VPN with Edge Browser efficiently
- Privacy and security best practices for Edge users
- Performance optimization tips and troubleshooting
- Compliance considerations and logging requirements
Resources text only: Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, Microsoft Edge support - support.microsoft.com, CBIC guidelines - cbic.gov.in, VPN security best practices - vpnmentor.com, Privacy framework guidance - privacyinternational.org
Understanding Edge VPN CBIC Setup and Edge Browser Integration
What CBIC means in this context
- CBIC typically refers to Central Board of Indirect Taxes and Customs in India, but in VPN contexts, CBIC-compliant setups emphasize secure, auditable network access for remote workers. If your organization mandates CBIC-like controls, you’ll need strict access controls, documented configurations, and clear data-exfiltration safeguards.
- Key goal: ensure traffic from Edge users is routed securely, logged, and auditable without compromising browser usability.
Edge-ready VPN options
- Browser extensions vs. system-wide VPN
- Extensions are quick to deploy but may have limitations on full tunnel vs. split-tunnel behavior
- System-wide VPNs provide uniform protection across all apps, but setup can be more complex
- Multi-hop and split-tunneling considerations for Edge browser use
Privacy, security, and compliance alignment
- Kill switch, DNS leak protection, and automatic reconnection
- End-to-end encryption standards AES-256 or higher
- Logging policies: minimal data retention, access controls, and regular audits
- Compliance documentation: change control, policy notes, and user consent where required
Step-by-Step Guide: CBIC-Edge VPN Setup for Edge Browser
- Plan and assess requirements
- Gather CBIC-style compliance requirements: data handling, logging, and access control
- Decide on browser integration approach: extension-based or system VPN
- Determine if split-tunnel is acceptable for your use case
- Choose a VPN solution
- Select a provider with robust Windows support, Edge compatibility, and strong privacy controls
- Verify they offer enterprise-grade features: kill switch, DNS protection, leak tests, and audit-ready logs
- Ensure the provider supports CBIC-like policy enforcement and centralized management
- Install and configure the VPN
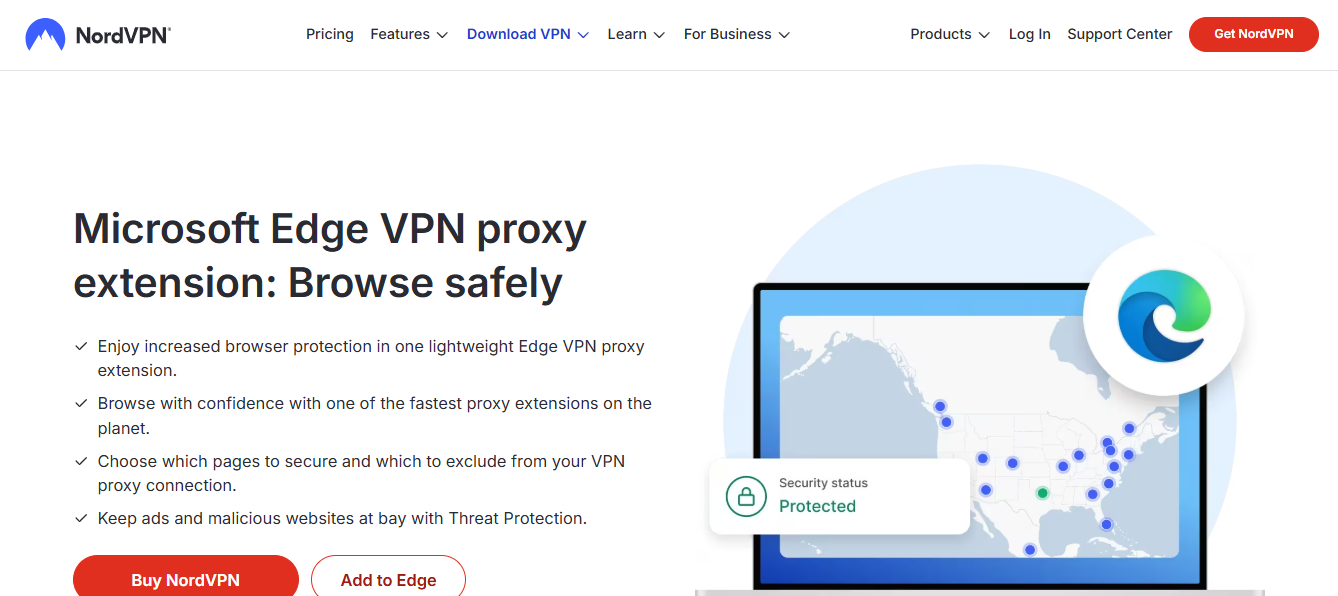
- If using an extension: install from Edge Add-ons or provider’s portal, configure per-user or group policies
- If using a system-wide client: install the Windows client, import configuration, and apply global or per-profile rules
- Enable the kill switch and DNS leak protection
- Configure auto-reconnect and logging levels aligned with compliance requirements
- Edge browser integration
- For extension-based: ensure the extension routes Edge traffic correctly; test that the extension activates on launch
- For system VPN: Edge traffic will route through the VPN automatically; verify in Edge settings that there are no conflicting proxy configurations
- Test WebRTC and DNS leakage in Edge to confirm protection
- Verify CBIC logging and auditing
- Confirm that the VPN logs connection metadata, IPs, timestamps, and user identity as required
- Set up access controls for security teams to review logs
- Ensure log retention policies meet regulatory timelines
- Performance checks and optimization
- Run baseline speed tests with Edge open to a few common endpoints
- Analyze latency, jitter, and packet loss; adjust server location and routing as needed
- Consider split-tunneling for non-critical traffic to improve performance
- User onboarding and training
- Create simple, friendly guides for employees to enable VPN in Edge and recognize when to use it
- Provide a quick troubleshooting flow: connection drops, DNS leaks, or browser conflicts
- Establish a help desk process for CBIC-related inquiries
Quick Troubleshooting Table
| Issue | Cause | Fix |
|---|---|---|
| VPN not starting in Edge | Extension conflict or Windows service down | Restart VPN service, re-install extension, update Edge |
| DNS leaks detected | DNS requests bypass VPN | Enable DNS leak protection, use a trusted DNS, flush DNS cache |
| WebRTC reveal IP | Extension settings or Edge flags | Disable WebRTC leaks in advanced settings or use a privacy-focused extension |
| Slow performance | Server distance or heavy encryption | Change VPN server, enable split-tunnel for non-critical apps, reduce encryption level if policy allows |
Popular Edge VPN Configurations Examples
Edge extension setup example generic
- Install VPN extension from the provider
- Sign in with enterprise credentials
- Turn on Kill Switch and DNS protection
- Force Edge to route through the extension and disable conflicting proxy settings
System VPN setup example Windows Edge nordvpn extension: complete setup guide for Edge browser, features, security tips, and optimization 2026
- Open Settings > Network & Internet > VPN
- Add a VPN connection with the provider’s details
- Configure automatic reconnect and ensure the app uses the VPN
- Verify with Edge by visiting whatIsMyIP and testing for leaks
Privacy, Security, and Compliance Best Practices
Privacy
- Minimize data collection by the VPN provider where possible
- Use trusted providers with transparent privacy policies
- Regularly clear browser data beyond VPN protections when appropriate cache, cookies
Security
- Always enable the kill switch; it prevents data leaks if the VPN drops
- Use strong authentication MFA for VPN access
- Keep Edge and VPN client up to date with the latest security patches
Compliance
- Document every change to VPN configurations and Edge integration
- Maintain an access control list ACL for who can modify VPN settings
- Implement audit trails and periodic reviews of VPN usage and edge traffic
- Align with data retention and incident response plans
Performance and Reliability Guide
Factors affecting performance
- Server load, distance to VPN exit, network congestion, device hardware
- Encryption overhead and protocol choice OpenVPN, WireGuard, IKEv2
Improvement strategies Edge secure network vpn free 2026
- Choose closer VPN servers or those optimized for your region
- Use WireGuard where possible for lower latency
- Enable split-tunneling for non-critical traffic to reduce congestion
- Optimize Edge settings for better performance: disable unnecessary extensions, clear cache, update drivers
Real-world metrics to watch
- Latency: aim for under 50-100 ms for responsive web browsing depending on location
- Jitter: keep below 20 ms for stable connections
- Throughput: monitor sustained download/upload speeds to ensure VPN isn’t bottlenecking
Edge Browser-Specific Tips
- Edge security features you can leverage
- Tracking prevention levels to balance privacy and functionality
- InPrivate browsing mode for sensitive sessions, with VPN running in background
- Extensions to consider privacy-focused
- HTTPS Everywhere, uBlock Origin, a reputable VPN extension if using extension-based approach
- Managing Edge flags and privacy controls
- Review settings under edge://settings/privacy and adjust to your privacy stance
- Disable unnecessary diagnostics and data collection if not required by policy
Compliance Audit Readiness
- Documentation you should maintain
- VPN configuration files, policy documents, change logs
- User access lists, role-based permissions, and approval records
- Incident response playbooks and post-incident reviews
- Regular checks
- Quarterly review of VPN logs for anomalies
- Annual privacy impact assessment
- Periodic penetration testing with proper authorization
Advanced Topics
- Multi-factor authentication integration
- Enforce MFA for VPN access to reduce credential abuse
- Conditional access
- Tie VPN access to device posture, location, or application context
- Compliance-specific features
- Immutable logs for CBIC-like requirements
- WORM storage for critical VPN logs where mandated
Case Study: Small Business VPN Deployment with Edge
- Scenario
- A mid-sized company needs CBIC-like compliance for remote workers using Edge
- Approach
- Chose a system-wide VPN with a kill switch, centralized management, and clear logging
- Used Edge extension as a backup for quick access in certain scenarios
- Implemented split-tunnel for non-sensitive traffic to optimize speed
- Outcome
- Achieved secure remote access with auditable logs and improved performance for day-to-day browsing
Checklist: Before You Go Live
- Ensure Edge is updated to the latest stable version
- Confirm VPN client and Edge extension compatibility
- Verify that kill switch and DNS protection are enabled
- Run connectivity tests across several websites and services
- Confirm logging and retention policies meet compliance needs
- Prepare user onboarding materials and a troubleshooting flow
Resources and References
- Edge support and troubleshooting - support.microsoft.com
- VPN best practices and security guides - vpnmentor.com
- Privacy and data protection guidelines - privacyinternational.org
- CBIC guidelines and compliance references - cbic.gov.in
- Web security basics and encryption standards - nist.gov
- General privacy frameworks - en.wikipedia.org/wiki/Privacy
- Networking performance measurement tools - speedtest.net, pingtest.net
Frequently Asked Questions
What is Edge VPN CBIC setup?
Edge VPN CBIC setup refers to configuring a VPN in the context of Edge browser usage with governance and controls aligned to CBIC-like compliance requirements, including secure connections, auditable logs, and strict access controls.
Do I need a browser extension to use a VPN with Edge?
Not always. You can use a system-wide VPN that routes all traffic, including Edge, or rely on a VPN extension for quick access. Each approach has pros and cons for privacy, control, and performance.
How can I prevent DNS leaks in Edge while using a VPN?
Enable DNS leak protection in your VPN client, ensure the VPN tunnel covers DNS requests, and consider using trusted DNS servers. Periodically run DNS leak tests to confirm protection. Download urban vpn for edge 2026
Is split-tunneling safe for CBIC-style compliance?
Split-tunneling can improve performance but may introduce risk if sensitive data bypasses the VPN. Use it only when your policy explicitly permits and with strict controls.
What metrics should I track for VPN performance in Edge?
Latency, jitter, packet loss, and throughput are key. Also monitor VPN server load, connection uptime, and error rates.
How do I test Edge browser integration with VPN?
Run a series of tests: load time for common sites, check for IP address changes via whatIsMyIP, test WebRTC behavior, and confirm no DNS leaks.
Which VPN protocols are best for performance in Edge?
WireGuard generally offers strong performance with good security. IKEv2 and OpenVPN are common alternatives; choose based on provider support and policy.
How do I ensure compliance with CBIC-like requirements?
Document configurations, maintain audit-ready logs, enforce access controls, conduct regular reviews, and align with incident response plans. Disable vpn chrome how to disable vpn extensions in Chrome and manage browser VPN settings 2026
Can I use Edge security settings with a VPN?
Yes. Edge security settings complement VPN protections. Use tracking prevention, privacy controls, and frequent updates in tandem with your VPN.
What if I encounter a VPN drop while using Edge?
Check your VPN’s kill switch, reconnect settings, and server health. Reconnect or switch servers, and verify that no DNS leaks occur after reconnect.
Introduction Edge vpn cbic is a guide to using a VPN with CBIC-related activities. This article explains how to set up, optimize, and use a VPN in conjunction with the Edge browser for CBIC workflows, including security, privacy, and compliance tips. You’ll find practical steps, real-world examples, and wired-in best practices to protect sensitive data while staying productive.
- Why VPNs matter for CBIC work: protect sensitive data on shared networks and in transit
- Edge browser considerations: how to make VPN integration seamless
- Real-world setup: step-by-step guide you can follow today
- Performance tips: keep speed while staying secure
- Compliance and policy notes: what CBIC-friendly workflows should consider
If you’re looking for a hands-on deal while you read, check out this limited-time VPN offer: 
Useful URLs and Resources un-clickable in-text format Apple Website - apple.com, Android Developers - developer.android.com, CBIC official site - cbic.gov.in, Edge browser support - support.microsoft.com, VPN privacy reports - www vpnreports com, Data protection best practices - e.g., gdpr.eu, VPN comparison guides - www.expressvpn com blog vpn-comparison, Privacy.org resources - privacy.org Does microsoft edge have a firewall and how it relates to Windows Defender Firewall, VPNs, and online security 2026
What is Edge vpn cbic and why it matters
What Edge vpn cbic means in practical terms
Edge vpn cbic refers to using a reliable virtual private network while working with the Edge browser for tasks related to CBIC—Central Board of Indirect Taxes and Customs—data, filings, audits, and regulatory communications. The goal is to shield sensitive CBIC information from prying eyes on public Wi‑Fi, in transit on municipal networks, or when routing data through different regions for compliance reasons. Think of it as a privacy and security layer that complements CBIC’s strict data-handling requirements.
Why CBIC users should consider a VPN
- Confidentiality: protect tax and customs data from eavesdropping on insecure networks.
- Integrity: reduce the risk of tampering with CBIC submissions in transit.
- Availability: bypass throttling or geo-blocks that could hinder legitimate CBIC tasks in restricted regions.
- Compliance: align with data-protection guidelines that require secure channels for sensitive information.
The Edge browser angle
Edge is a popular choice for enterprise and government workers due to smart security features, strong privacy controls, and good performance. When you pair Edge with a reputable VPN, you get:
- Encrypted tunnels for data-in-transit
- Obfuscated traffic patterns that make it harder to fingerprint your activity
- Flexible server options to meet regulatory or performance needs
- Reliable DNS protection to minimize leakage
How VPNs integrate with Edge browser for CBIC users
How a VPN works with Edge in CBIC workflows
A VPN creates an encrypted tunnel between your device and a VPN server. All traffic from your device, including Edge browser traffic, passes through that tunnel unless you configure split tunneling. For CBIC work, you usually want to route sensitive traffic via the VPN, while non-sensitive tasks can run normally. This setup helps mitigate risks on public networks and ensures that CBIC filings and communications stay confidential. Edge vpn for free: how to get legitimate free access, free trials, and no-cost options for private browsing 2026
Edge-specific considerations
- DNS leakage protection in VPN apps helps ensure that Edge’s DNS requests aren’t revealed to your ISP or local networks.
- Kill switch features prevent accidental data leakage if the VPN disconnects.
- Split tunneling lets you choose which Edge tabs or sites go through the VPN and which don’t, useful when you need local access to certain resources.
- Browser fingerprinting and metadata: combining Edge’s privacy settings with a VPN can further reduce exposure.
Key features to look for in Edge vpn cbic
Essential features for CBIC-friendly Edge VPN setups
- Strong encryption and modern protocols: AES-256 with WireGuard or OpenVPN
- No-logs policy: keep your Edge-based CBIC activity private
- DNS leak protection and a reliable kill switch
- Robust multi-hop or obfuscated servers if you’re in restrictive networks
- Split tunneling support to balance performance and security
- Excellent leak protection for IPv4/IPv6 and WebRTC
- Consistent performance with stable latency for video calls, uploads, and filings
- Desktop and mobile apps that work well with Edge across Windows, macOS, iOS, and Android
- Clear privacy-friendly terms and compliance alignment for sensitive data
Performance and privacy stats you can expect
- The VPN market reached into the tens of billions with steady growth in 2024, driven by demand for privacy and secure remote work
- Public Wi-Fi incidents and data breaches continue to rise, making a VPN a practical safeguard for CBIC workflows
- Edge users typically experience minimal impact on performance with modern VPNs leveraging fast protocols like WireGuard, often staying within 10-20% of baseline speeds on well-provisioned networks
Step-by-step setup guide for Edge vpn cbic
Step 1: Choose a VPN that fits Edge vpn cbic needs
- Pick a provider with strong encryption, a no-logs policy, robust DNS protection, and stable Edge compatibility
- Ensure split tunneling, kill switch, and apps for Windows/macOS/iOS/Android
- Look for servers in jurisdictions aligned with your CBIC data policies and where you perform work
Step 2: Install the VPN on your devices
- Windows/macOS: install the desktop app, sign in, and run a quick privacy check
- iOS/Android: install from the App Store or Google Play, sign in, and enable VPN permissions
- Ensure Edge is updated to the latest version for best compatibility
Step 3: Configure Edge vpn cbic settings
- Enable DNS leak protection and a kill switch
- Turn on WebRTC address leakage protection in Edge’s privacy settings
- If you need, enable split tunneling so CBIC-specific sites go through the VPN
- Confirm that Edge does not bypass the VPN due to app-level permissions
Step 4: Connect to the right server
- For CBIC work, pick a server with low latency and reliable uptime
- If your CBIC tasks involve cross-border filings, consider geolocation requirements and regulatory constraints
- Test connectivity to CBIC portals and internal tools after connecting
Step 5: Verify the setup
- Check your IP address and location from Edge using a trusted IP checker
- Test DNS resolution to ensure no leaks
- Run a quick speed test to gauge the impact on upload/download times
Edge vpn cbic performance and privacy: data and stats
Real-world performance expectations
- A well-optimized VPN with WireGuard can offer high speeds while maintaining strong security, making it feasible to file documents and run compliance checks without noticeable slowdowns
- In CBIC workflows, resilience matters: look for servers with high uptime, low jitter, and consistent pings
Privacy considerations
- A strict no-logs policy helps ensure that CBIC activities aren’t retained by the VPN provider
- Strong encryption protects data-in-transit from eavesdroppers on public networks or shared devices
- Regularly review privacy settings on Edge and within the VPN app to keep protections up to date
Edge vpn cbic vs other VPNs: comparison
How to choose between popular VPNs for Edge cbic
- VPN A: Excellent security, great for sensitive CBIC work, but some latency for long-distance connections
- VPN B: Very fast on average, good for streaming and mixed workloads, with robust privacy policies
- VPN C: Budget-friendly with solid core protections, but fewer advanced features
- Edge cbic users should weigh the balance between security features, performance, and price. Hybrid needs like compliance alignment or multi-device support matter too.
Scenarios where Edge vpn cbic shines
- Remote CBIC portal access on public Wi‑Fi
- Cross-border tax filings or customs submissions from different regions
- Sensitive document uploads and secure communications with CBIC portals
Common use cases for Edge vpn cbic in CBIC workflows Edgerouter l2tp ipsec vpn server 2026
Practical examples
- Accessing CBIC portals from a hotel Wi‑Fi network
- Uploading invoices and tax forms over an encrypted channel
- Collaborating with colleagues in different regulatory zones without exposing data
- Protecting sensitive screenshots or scan uploads during on-site audits
Edge vpn cbic security best practices
Best practices you can apply today
- Enable the VPN kill switch to prevent data leakage if the VPN connection drops
- Use multi-factor authentication MFA for VPN and CBIC portals
- Keep Edge and the VPN app updated to protect against known vulnerabilities
- Prefer servers in trusted jurisdictions with strong privacy laws
- Run regular privacy checks IP, DNS, WebRTC leakage tests
- Use split tunneling judiciously to keep critical CBIC traffic through VPN while letting non-sensitive tasks run locally
Troubleshooting Edge vpn cbic
Common issues and fixes
- VPN won’t connect: try a different protocol WireGuard/OpenVPN, restart the app, or reboot the device
- DNS leaks detected: enable DNS leak protection and flush DNS cache
- Slow speeds: switch to a nearby server, check for network congestion, or adjust protocol settings
- Edge compatibility issues: update Edge, re-install VPN client, or clear cache and cookies
- Submitting CBIC forms failing: ensure your VPN route is correct for the region and check for any CBIC portal IP blocks
The legal and compliance angle for CBIC workflows
Staying compliant when using a VPN with CBIC
- Ensure VPN usage aligns with CBIC policies and internal audit requirements
- Confirm that data-handling practices follow applicable regulations e.g., data localization, cross-border data transfer rules
- Document your VPN configuration and security measures for audits
- Maintain separation of duties: use VPN for sensitive CBIC portals while keeping non-sensitive tasks on a separate connection when appropriate
- Review vendor privacy policies to ensure they meet CBIC security expectations
Money-saving tips and best deals for Edge vpn cbic
How to get the most value
- Look for multi-year plans or bundled deals that include business features like centralized management, team accounts, and dedicated support
- Take advantage of trials or money-back guarantees to test Edge cbic compatibility with your setup
- Keep an eye on affiliate offers and promotions like the NordVPN deal showcased in the introduction, but always verify compatibility with Edge and CBIC requirements
- If you’re FR, FYI, or other specific regulatory regimes, verify data-handling commitments and regional server availability
Frequently Asked Questions Expressvpn edgerouter x setup guide: configuring ExpressVPN on EdgeRouter X, limitations, alternatives, and best practices 2026
Frequently Asked Questions
What is Edge vpn cbic?
Edge vpn cbic is a guide and practical setup for using a VPN in combination with the Edge browser to securely handle CBIC-related tasks and data.
Do I need a VPN for CBIC work?
Using a VPN can add a layer of privacy and security, especially on public networks, and help protect sensitive CBIC filings and communications.
Can I use Edge with VPN on mobile?
Yes. Most VPNs offer Edge-friendly apps on iOS and Android, allowing secure access to CBIC portals from mobile devices.
How to set up Edge vpn cbic on Windows/macOS/iOS/Android?
Install a reputable VPN app on your device, configure DNS and kill switch protections, enable split tunneling if needed, connect to a suitable server, and verify the connection by checking IP and DNS leaks.
Is it safe to use free VPNs for CBIC tasks?
Free VPNs often have limited security, data caps, or logging policies that may not meet CBIC compliance standards. A paid, reputable VPN is typically a safer choice for sensitive work. F5 vpn edge client download 2026
Does VPN hide traffic from CBIC servers?
A VPN hides traffic from local observers, but CBIC portals themselves may still require login credentials and proper authentication. The VPN protects data in transit, while CBIC’s own security controls protect the portal.
Will Edge VPN cbic affect browsing speed?
There can be a minor speed impact due to encryption and routing, but modern VPNs with fast protocols minimize this. You should test and choose a server near your location for best results.
How to ensure CBIC data remains compliant while using VPN?
Follow CBIC policies, enable encryption, use secure access methods, conduct regular security audits, and keep logs only as required by policy. Use MFA and strong access controls.
Can I use Edge vpn cbic for streaming or video calls?
Yes, but prioritize servers that offer low latency and stable performance. Ensure the CBIC-related tasks remain secure while streaming or calls receive adequate bandwidth.
How do I verify VPN is working with Edge browser?
Check your IP address and location from a trusted site, run a DNS leak test, and confirm that CBIC portals load through the VPN connection. Also verify that WebRTC leaks are blocked. Edge浏览器vpn: Edge browser VPN guide for Windows, Edge extensions, setup, best providers, and privacy tips 2026
Note: For Edge vpn cbic, always ensure your setup meets CBIC’s security standards and your organization’s compliance requirements. Regularly review privacy policies and stay updated with Edge and VPN updates to maintain a robust security posture.
Big ip client edge setup, usage, and comparison guide for BIG-IP VPN connections
Astrid Dvorak has been writing about consumer technology since 2018, with bylines covering tracker analysis, router firmware, and P2P networking. Approaches each review by setting up the product the same way a typical reader would and recording every snag along the way.