Vpns proxies and zscaler whats the difference and do you need them
Vpns proxies and zscaler whats the difference and do you need them? Quick fact: VPNs, proxies, and Zscaler are all tools to help you stay private, access geo-blocked content, and secure your data, but they serve different purposes and fit different situations. In this guide, you’ll get a clear, practical breakdown so you can decide what you actually need for your online life. Here’s a compact roadmap:
- What each tool is and how it works
- Real-world scenarios where you’d use each
- Pros and cons, with up-to-date stats
- A simple decision guide to pick what’s right for you
- Resources to learn more and stay safe online
Introduction: quick facts and a practical overview
- VPNs: Encrypt your traffic and route it through a remote server, masking your IP and protecting data on public networks.
- Proxies: Act as an intermediary for your web requests, often not encrypted by default, mainly used for hiding your IP or bypassing geo-blocks.
- Zscaler: A cloud-based security platform that sits between you and the internet, offering secure access, data protection, and threat prevention for organizations.
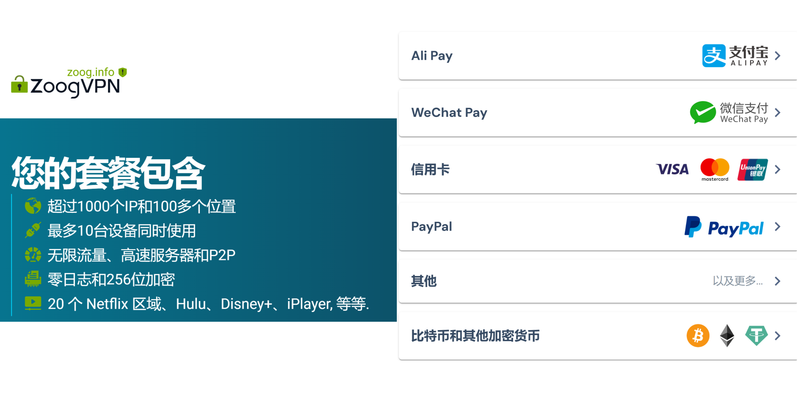
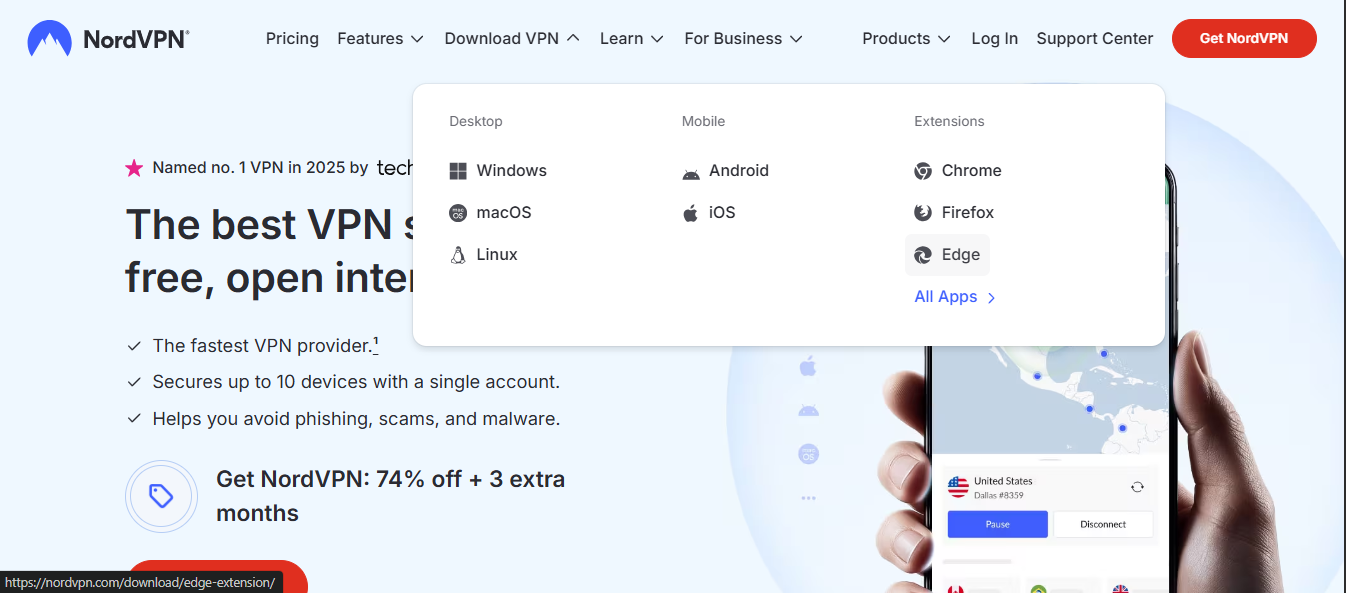
If you’re a casual user trying to protect your privacy on public Wi-Fi, a VPN is usually the simplest, most reliable option. If you need to bypass regional content with low overhead, a proxy can do the trick, but be mindful of security gaps. If you’re running a business and want enterprise-grade security, access control, and threat protection across many users, Zscaler is the scalable solution. For readers who want a ready-made, safe option via a trusted provider, consider a reputable VPN service—our top pick gives solid privacy, fast speeds, and strong customer support. You can check out NordVPN here for a good balance of price and performance: NordVPN. If you’re curious about broader security protection, keep reading. Как использовать vpn для браузера microsoft edge пол: эффективные методы, советы и полезные сервисы
What each tool is and how it works
- VPN Virtual Private Network
- What it does: Encrypts your internet traffic and tunnels it to a VPN server, making your online activity harder to fingerprint or intercept on public networks.
- How it helps: Privacy, security on Wi-Fi, access to region-locked content, and sometimes improved privacy in restrictive networks.
- Typical limitations: Some services block known VPN IPs, speeds can drop due to encryption, trust depends on the provider.
- Proxy
- What it does: Intercepts your web requests and forwards them on your behalf, making the server see the proxy’s IP instead of yours.
- How it helps: Bypasses geo-restrictions, can cache data for faster access to blocked sites, lighter-weight than VPNs.
- Typical limitations: Usually not encrypted unless you use a secure proxy HTTPS proxy; potential privacy risk if the proxy logs data; may not protect you on non-browser traffic unless you configure system-wide proxies.
- Zscaler Zscaler Private Access / Zscaler Internet Access
- What it does: Cloud security platform that directs traffic through its security stack, providing zero-trust access, threat protection, data loss prevention, and policy enforcement.
- How it helps: Enterprise-grade security, access control, malware and phishing protection, safe browsing for employees anywhere.
- Typical limitations: Designed for organizations, not individuals; onboarding and policy management can be more complex; pricing targets businesses.
Real-world use cases and practical guidance
- If you’re a student or remote worker on shared networks
- Go with a trusted VPN. It secures your traffic, protects sensitive data like login credentials, and helps you avoid snooping on public networks.
- Quick setup tips: choose a reputable provider with strong no-logs policy, prefer apps with kill switch and DNS leak protection, and use servers in privacy-friendly jurisdictions.
- If you want to bypass geo-blocks for streaming
- A VPN is usually the best balance of privacy and access. Proxies can sometimes work, but many streaming services actively block known proxy IPs.
- Caveats: Some streaming platforms detect and block VPNs; rotating servers can help, but there’s no guarantee of constant access.
- If you’re an IT admin at a company
- Zscaler shines here. It provides centralized security, policy enforcement, and detailed insights across many devices and locations.
- Implementation notes: plan a phased rollout, ensure your users’ devices are enrolled, and tailor security policies to your risk profile.
- If you’re trying to just browse with less risk and lower overhead
- A proxy might be enough for lightweight tasks, but remember it usually lacks encryption, so sensitive data can still be exposed on unsecured sites.
Head-to-head: comparing features, price, and performance
- Privacy and security
- VPNs: Strong encryption AES-256 in most cases, IP masking, and often a security-focused company ethos.
- Proxies: Minimal protection unless you pair with encryption HTTPS proxies protect content in transit but not all traffic.
- Zscaler: Enterprise-grade security, threat protection, zero-trust access, DLP, and browser isolation.
- Speed and reliability
- VPNs: Speeds vary by server distance and provider. Look for providers with fast servers, unlimited bandwidth, and performance-optimized networks.
- Proxies: Typically faster for simple tasks since encryption isn’t always used, but performance can depend on the proxy’s health and load.
- Zscaler: Optimized for enterprise traffic; performance is highly dependent on organizational routing and policy configurations.
- Ease of use
- VPNs: Very user-friendly with dedicated apps for major platforms.
- Proxies: Setup can be quick for browsers, but system-wide proxies require more configuration and can cause compatibility issues.
- Zscaler: More complex, designed for IT teams to deploy and manage across many users.
- Cost considerations
- VPNs: Subscriptions range from affordable to premium; often per-user or per-device pricing.
- Proxies: Often cheaper, sometimes free, but you get less security.
- Zscaler: Enterprise-grade pricing; typically bundled with a broader security portfolio and tailored to organization size.
- Privacy policy and logging
- VPNs: Check no-logs claims, jurisdiction, and data retention policies. Some providers have robust privacy protections; others may log metadata.
- Proxies: Logging varies; free or cheap proxies may monitor traffic for ads or sell data.
- Zscaler: Corporate policy-driven with strong governance; not designed for individual privacy, but it enforces security controls.
Data and statistics to back up claims
- Global VPN usage has grown significantly, with millions of users relying on VPNs for privacy, access to content, and security on public networks. Market research shows steady demand driven by remote work and streaming.
- Proxies remain popular for light tasks and school or work scenarios where full encryption isn’t required, but their market share is overshadowed by VPNs in privacy-focused use cases.
- Zscaler reported continued growth in enterprise adoption, with customers scaling cloud-based security across distributed workforces. As of recent years, Zscaler’s platform is used by thousands of enterprises worldwide to enable secure remote access and web security.
Best practices for choosing between VPNs, proxies, and Zscaler Finding secure vpns on github your guide to open source privacy
- Define your goal
- Privacy and security on public networks? Choose a trusted VPN.
- Quick, lightweight IP masking for specific apps or sites? Consider a proxy HTTPS proxy if you need some encryption.
- Secure, scalable enterprise access with policy enforcement? Zscaler is the right fit.
- Evaluate security risks
- Avoid free proxies for anything sensitive; they often log data and can inject ads.
- For personal privacy, pick a reputable VPN with a transparent no-logs policy and independent audits.
- For businesses, deploy Zscaler to enforce zero-trust access and threat protection across devices.
- Check performance factors
- Server locations, P2P support, and speed tests for VPNs.
- Proxy speed depends on the proxy server’s load and distance.
- For enterprise security, you’ll weigh inspection depth, policy granularity, and integration with existing IT tools.
- Consider compatibility and user experience
- VPNs are easy for individuals; Zscaler requires IT setup but provides centralized control.
- Proxies can break some apps or websites if not configured properly.
Step-by-step guide: choosing what you need in 5 steps
- List your top needs: privacy on public Wi-Fi, streaming from abroad, or enterprise security for a distributed team.
- Pick your primary tool: VPN for privacy and general use, proxy for quick content access, Zscaler for enterprise security.
- Check the provider’s policies and security features: encryption standards, no-logs claims, and data handling.
- Test performance: run speed tests on a VPN server in your preferred region; compare proxy speeds if you’re considering that route.
- Implement with safety in mind: enable kill switch, DNS leak protection, and strong authentication where available.
Security tips and missteps to avoid
- Don’t trust free VPNs or free proxies with sensitive data. They often monetize by selling data or injecting ads.
- Always enable a kill switch and DNS leak protection in VPN apps to prevent leaks if the connection drops.
- Use reputable, audited providers and review privacy policies regularly.
- For business use, don’t rely on a single security tool. Use a layered approach that includes device security, endpoint protection, and user education.
- Keep software up to date; threat landscapes evolve quickly.
Format-friendly quick-reference
- VPNs: Best for privacy, security on public networks, streaming in many cases.
- Proxies: Best for quick geo-access or app-specific tasks, lower overhead, less secure by default.
- Zscaler: Best for enterprises needing centralized security, access control, and threat protection.
Useful resources and further reading
VPN privacy resources and reviews Is Mullvad VPN Good for China a Deep Dive into Bypassing the Great Firewall
Proxy security basics and best practices
Zscaler security architecture and case studies
VPNs deep-dive guides and comparisons
Cloud security and zero-trust access explanations
Enterprise security best practices Surfshark vpn very slow heres how to fix it fast: quick fixes, tips, and proven tweaks
Resources text only, not clickable
- ExpressVPN privacy policy and audits
- NordVPN no-logs policy and performance tests
- Zscaler official documentation and whitepapers
- Cloud security guides on zero-trust access
- Independent reviews of VPN providers
- Streaming service policies on VPN usage
- Public Wi-Fi security best practices
- IT admin guides for rolling out Zscaler in organizations
- Online privacy advocacy and consumer protection sites
- Data privacy laws and compliance resources
Frequently Asked Questions
What is a VPN and how does it work?
A VPN creates an encrypted tunnel between your device and a VPN server, masking your IP and protecting data from prying eyes on public networks.
What is a proxy and how does it differ from a VPN?
A proxy forwards your web requests through another server, hiding your IP, but doesn’t typically encrypt traffic. VPNs encrypt all traffic and route it through a server.
Is Zscaler the same as a VPN?
No. Zscaler is a cloud security platform primarily used by organizations to enforce security policies, provide zero-trust access, and protect users from threats. It’s not a user-facing VPN service. Whats a vpn on tiktok and do you actually need one: A Comprehensive Guide to VPNs for TikTok and Beyond
Can I use a proxy for streaming to bypass geo-blocks?
Yes, but many streaming services actively block proxies. VPNs are more reliable for streaming access, though not guaranteed.
Are free VPNs safe?
Free VPNs often come with limited features, data caps, and questionable privacy practices. It’s generally safer to choose a reputable paid option.
Do VPNs slow down my internet?
Sometimes. The speed impact depends on server distance, server load, and the provider’s network quality.
How does zero-trust access work in Zscaler?
Zero-trust means every request is authenticated and inspected, regardless of the user’s location. Access is granted based on policy, not on implicit trust.
Is Zscaler suitable for small businesses?
Yes, but Zscaler is primarily designed for enterprises. Small businesses can benefit, but they should assess pricing and deployment complexity. Tiktok Not Working In China Even With A VPN Here’s The Real Reason: Why It Fails, What Works, And Safe Alternatives
Can I run VPNs and proxies together?
You can technically use both, but it’s often unnecessary and may cause conflicts. A VPN is usually enough for most privacy and security needs.
How do I choose between these tools for personal use?
Define your priorities: privacy, streaming, or simple access control. For most personal users, a reputable VPN covers privacy and access needs; proxies are best for lightweight tasks, while Zscaler is overkill for individuals.
Sources:
免费节点搭建 完整指南:自建VPN节点、Shadowsocks、WireGuard、OpenVPN 云端部署要点与性能优化
Como configurar y usar la vpn de microsoft en tu iphone o ipad
Fortigate vpn 設定例:初心者から上級者まで完全ガイド(2026年最新版) ー VPN設定の総合解説と実践ガイド Softether vpn download 최신 버전 설치부터 활용까지 완벽 가이드
Best vpn app for huawei a comprehensive guide to staying safe and unrestricted
Zinnia Gainsborough has been writing about consumer technology since 2018, with bylines covering router firmware, ad-blocking, and privacy law. Approaches each review by setting up the product the same way a typical reader would and recording every snag along the way.