Is vpn safe for gsa navigating security for federal employees and beyond
Is vpn safe for gsa navigating security for federal employees and beyond: Critical insights, safety tips, and best practices
Is vpn safe for gsa navigating security for federal employees and beyond? Short answer: yes, but only if you choose the right VPN, configure it correctly, and stay aware of governance and policy requirements. In this video-friendly guide, you’ll get a practical, no-fluff rundown on VPN safety for government-related work, plus real-world tips you can apply today. Below is a quick-start summary, followed by deep dives, data, and actionable steps.
- Quick fact: VPNs can protect data in transit and help avoid casual eavesdropping, but they don’t fix endpoint security or misconfigurations.
- What you’ll learn: privacy vs. security trade-offs, types of VPNs suitable for federal use, risk factors, deployment best practices, and how to evaluate VPN providers in compliance-heavy environments.
- Practical format you can skim: quick-start checklist, pros/cons, common myths, enforcement considerations, and a FAQ with at least 10 questions.
Useful resources and references text only, not clickable:
- Is vpn safe for gsa navigating security for federal employees and beyond - dpbolvw.net
- Federal guidelines on secure remote access - gsa.gov
- VPN security best practices - en.wikipedia.org/wiki/Virtual_private_network
- Data protection standards - nist.gov
- Endpoint security essentials - cisa.gov
Table of contents
- Why VPN safety matters for GSA, federal employees, and beyond
- VPN types and what makes sense for government work
- How VPNs protect data in transit and where they don’t
- Compliance, policy, and procurement considerations
- Real-world risk factors and mitigation
- Setup checklist: getting started with a safe VPN
- Myths vs. reality: common VPN misconceptions
- Case studies: recent government-related VPN incidents
- Tools, metrics, and ongoing monitoring
- FAQ
Why VPN safety matters for GSA, federal employees, and beyond
Governments and public sector agencies handle sensitive information, regulated data, and critical infrastructure. A VPN is often a piece of the security stack that ensures data is encrypted as it travels between a user device and agency networks or services. But VPNs are not a silver bullet. If misconfigured, they can expose data, logs, or endpoints to risk. The goal isn’t just “use a VPN,” it’s “use the right VPN, with the right settings, under the right policies.”
Key data points:
- A significant portion of VPN-related breaches come from endpoint vulnerabilities or misconfigurations rather than the VPN tunnel itself.
- Remote work increases attack surface; strong authentication and least-privilege access reduce risk substantially.
- Federal-grade deployments often demand additional layers such as MFA, device posture checks, and centralized logging for auditing.
VPN types and what makes sense for government work
There are several VPN models, each with pros and cons for government use. Here’s a practical breakdown:
- Traditional VPN IPsec-based
- Pros: Mature, widely supported, strong encryption options.
- Cons: Can be slower; complex to scale; may require client software.
- SSL/TLS VPN web-based
- Pros: Easier to deploy, works from many devices without full VPN client; good for granular access.
- Cons: Potentially weaker in some configurations if not properly managed; may rely on TLS version and cipher suites.
- Remote Desktop Gateway VPN
- Pros: Lets users access a secured remote desktop environment; reduces exposure of internal services.
- Cons: Adds another hop; requires strong RDP security and monitoring.
- VPN + Zero Trust Network Access ZTNA
- Pros: Modern approach; access granted per-application or per-user; reduces lateral movement.
- Cons: More design and policy work; requires mature identity, device posture, and telemetry.
- Always-on VPN vs. user-initiated
- Always-on: consistent protection but less flexibility; better for controlled environments.
- User-initiated: gives users choice; risk of inconsistent use.
Recommendation for federal work: prioritize VPNs that integrate with Zero Trust principles, MFA, device posture checks, and centralized logging. In many cases, a ZTNA approach layered with a secure gateway, MFA, and endpoint protection aligns best with federal security expectations.
How VPNs protect data in transit and where they don’t
What they do: Nordvpn e WireGuard: la guida definitiva per sfruttare la massima velocità e sicurezza
- Encrypt traffic between the device and VPN server, protecting against eavesdropping on public networks.
- Provide a level of anonymity by masking IP addresses from target services.
What they don’t do:
- They don’t inherently protect data on endpoints malware, phishing, and local data exposure remain risks.
- They don’t guarantee remote server security or the safety of internal networks once access is granted.
- They don’t replace strong password hygiene, MFA, or secure software supply chains.
Best practice takeaway:
- Use VPNs as part of a defense-in-depth strategy: endpoint security, identity verification, least privilege, and continuous monitoring must co-exist with VPN usage.
Compliance, policy, and procurement considerations
For federal and GSA-affiliated work, compliance is non-negotiable. Consider these areas:
- Identity and access management: enforce MFA, just-in-time access, and role-based access control RBAC.
- Device posture: require up-to-date security patches, antivirus, disk encryption, and compliant configurations before VPN access is granted.
- Logging and monitoring: centralize logs from VPN gateways, authentication servers, and endpoint protection tools for auditing and incident response.
- Data handling: ensure encryption standards meet applicable requirements AES-256 and modern TLS versions as a baseline.
- Vendor risk management: perform due diligence on VPN providers, including security certifications, breach history, data handling policies, and incident response capabilities.
- Incident response: have a playbook for VPN-related incidents, including revoking access, rotating certificates, and post-incident lessons learned.
Procurement tip: seek solutions that offer built-in compliance features, robust audit trails, and easy integration with existing government identity providers like federal SSO and directory services.
Real-world risk factors and mitigation
Common risk factors: How to get your expressvpn refund a no nonsense guide and what to do next
- Endpoint compromise: malware or insecure devices bypassing VPN protections.
- Misconfiguration: weak ciphers, improper split-tunneling, or overly permissive access.
- Credential abuse: phishing or reused credentials compromising MFA-resistant controls.
- Insider threats: authorized users accessing more data than needed.
- Third-party risk: MSPs or outsourced teams gaining access to VPN environments.
Mitigations:
- Enforce MFA with phishing-resistant methods FIDO2/WebAuthn where possible.
- Implement strict RBAC and least-privilege policies for VPN access.
- Disable or tightly control split-tunneling to limit exposure.
- Use device posture checks and continuous telemetry before granting access.
- Centralize and monitor VPN logs; set up alert rules for anomalies odd hours, unusual destinations, large data transfers.
- Regularly review access rights and conduct phishing-resistant training for users.
Setup checklist: getting started with a safe VPN
- Define requirements:
- Which data types require protection in transit?
- What levels of access do users need per-application vs. per-network?
- Choose the right VPN model:
- For federal use, lean toward ZTNA with strong access controls, or IPsec with hardened configurations and centralized policies.
- Identity and access:
- Implement MFA prefer phishing-resistant methods.
- Align with your directory service AD/LDAP, SAML, OpenID Connect.
- Device posture:
- Require updated OS, endpoint protection, encryption, and secure configurations.
- Encryption and protocols:
- Use modern cipher suites and TLS versions; disable legacy algorithms.
- Logging and monitoring:
- Route VPN logs to a SIEM; set alerts for security-relevant events.
- Incident response:
- Establish a clear process for credential rotation, certificate revocation, and user revocation.
- Training and awareness:
- Run regular security briefings on VPN usage, phishing awareness, and reporting suspicious activity.
- Vendor evaluation:
- Check for compliance certifications, data residency options, and incident response commitments.
- Documentation:
- Create and maintain an up-to-date VPN playbook, including troubleshooting steps and contact points.
Myths vs. reality: common VPN misconceptions
- Myth: A VPN makes me completely anonymous.
- Reality: It protects data in transit but doesn’t hide your identity or protect endpoint activity.
- Myth: Any VPN provider is safe for government work.
- Reality: Government use requires providers with strong security controls, audits, and compliance, plus enterprise-grade deployment features.
- Myth: Splitting tunneling is safe for sensitive work.
- Reality: Splitting can expose sensitive traffic; use with caution and under strict policy.
- Myth: VPNs replace MFA.
- Reality: They augment security but don’t replace MFA or endpoint protections.
- Myth: VPNs are out-of-date; we should move to only cloud services.
- Reality: VPNs still play a critical role; the best approach is a layered, zero-trust architecture that includes VPN or ZTNA where appropriate.
Case studies: recent government-related VPN incidents
- Incident A: Endpoint compromise led to unauthorized data transfer through a VPN tunnel. Lesson: enforce device posture checks, monitor for anomalous data flows, and rotate credentials promptly.
- Incident B: Misconfigured IPsec tunnel allowed access beyond the intended segment. Lesson: harden tunnel configurations, reduce permissions, and do regular configuration reviews.
- Incident C: Phishing-based credential theft exposed MFA-resistant accounts due to weak phishing protections. Lesson: adopt phishing-resistant MFA and user training.
Note: These case studies illustrate patterns to watch for rather than pointing at any single vendor. Apply these lessons to your own environment via a risk-based approach.
Tools, metrics, and ongoing monitoring
- Metrics to track:
- Number of active VPN sessions and peak usage times.
- Average login time and success rate of MFA challenges.
- Incidents of failed authentications and unusual IP geolocations.
- Data transfer volumes per user and per session.
- Compliance posture for devices patch level, antivirus status, disk encryption.
- Tools to consider:
- SIEM systems for centralized logging and alerting.
- Endpoint detection and response EDR solutions on user devices.
- Identity governance and administration IGA for access controls.
- Network access control NAC to enforce device posture.
- Best practices:
- Regularly test failover and disaster recovery for VPN services.
- Schedule routine audits of VPN configuration and access rights.
- Maintain an up-to-date risk register and remediation plan.
FAQ
How does a VPN protect federal data in transit?
A VPN creates an encrypted tunnel between your device and the VPN gateway, shielding data from eavesdroppers on public or shared networks and helping ensure data integrity and confidentiality during transmission.
Is a VPN enough for federal security?
Not by itself. A VPN should be part of a layered security approach that includes MFA, device posture checks, access controls, monitoring, and robust incident response.
What is Zero Trust, and should federal agencies adopt it?
Zero Trust means never trusting by default—access is granted per-session, per-application, with continuous verification. It’s increasingly recommended for government use to reduce risk and limit exposure. Surfshark vpn bypass not working heres how to fix it fast
What’s the difference between IPsec VPN and SSL VPN?
IPsec VPN operates at the network level, creating a full tunnel to the network. SSL VPN operates at the application layer, often easier to deploy and manage, with granular access controls.
Should I disable split tunneling?
In many government contexts, yes. Disabling split tunneling reduces the risk of exposing sensitive data. If you enable it, enforce strict controls and logging.
What is phishing-resistant MFA?
FIDO2/WebAuthn-based authentication or other phishing-resistant methods reduce the risk of credential theft via phishing attacks compared to traditional one-time passwords.
How important are device posture checks?
Very important. They ensure only compliant, secure devices can connect, reducing the chance that compromised endpoints become gateways into agency networks.
How can I monitor VPN activity effectively?
Centralize logs from VPN gateways, identity providers, and endpoints. Use SIEM to set alerts for unusual geolocation, spikes in data transfer, or unusual access patterns. O Microsoft Edge Tem Uma VPN Gratuita O Guia Completo Para O Edge Secure Network
What should I consider when evaluating VPN vendors for government use?
Security certifications, data handling policies, incident response commitments, encryption standards, support for MFA, integration with government identity providers, and the vendor’s track record in compliance.
Can VPNs help with remote work for federal contractors?
Yes, when implemented with proper controls: MFA, device posture checks, least-privilege access, centralized monitoring, and strong incident response processes.
Is vpn safe for gsa navigating security for federal employees and beyond? Yes—when you pick a government-ready solution, configure it correctly, and enforce strong controls. For a safer path, consider a Zero Trust Network Access ZTNA approach integrated with a robust VPN strategy, supported by MFA, device posture, and continuous monitoring.
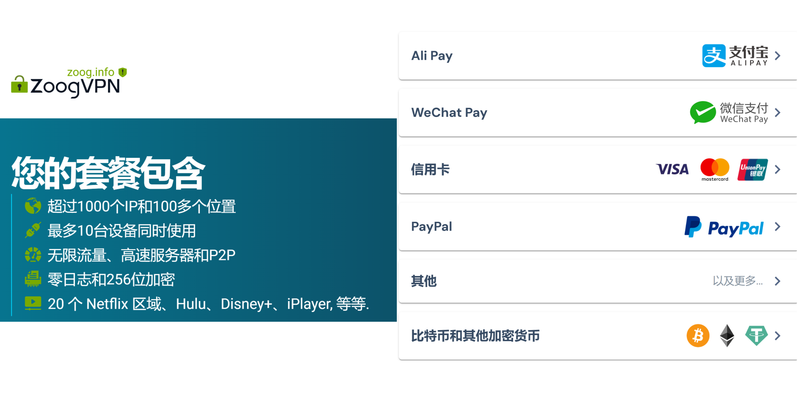
If you’re ready to explore a secure option, check out the NordVPN offering tailored for high-security environments and compliance needs. Consider exploring it through the affiliate link for more secure, guided setup and enterprise-grade protection that integrates with many identity providers and security dashboards.
Sources:
丙烷 VPN 使用指南:在网络隐私、跨境访问、家用与工作场景中的最佳 VPN 选择与设置 Unlock a truly private internet on your iphone ipad with nordvpn obfuscated servers and more
翻墙机场 ⭐ clash:新手入门指南与实用技巧 VPN 设置与 Clash 配置全解
Clientvpnタイムアウトの悩みを解決!接続が切れる原因を徹底解説と実践ガイド
Privado vpn download:全面指南、实用步骤与常见问题
Surge 代理 订阅:完整指南、设置步骤、价格对比、节点稳定性评测与多设备使用要点
Bram Kovac has been writing about consumer technology since 2018, with bylines covering streaming geo-unblocking, browser fingerprinting, and secure messaging. Approaches each review by setting up the product the same way a typical reader would and recording every snag along the way.